Internet is growing rapidly all across the globe.
Simultaneously there are continues research is going all across to find out various innovative ways to attack your existing computing environment. In a scenario where internet and computing environment has become a common place in cyber world, Illegal operation on your environment using internet has also become common. According to Forbes, the global cyber security market reached $75 billion for 2015 and is expected to hit $170 billion in 2020 and the cyber insurance market would be $14 billion. The threat is advancing quicker than we can keep up with it. The threat changes faster than our idea of the risk.
One of the most unpredictable instances of Cyber crime is constantly evolving risk factor. The traditional approach of protecting your computing environment is almost obsolete now. It is no more restricted to virus threat of data format risks; it is beyond that and in much more complex in nature. There are incidents that an attack has not only crated a huge financial damage, in some cases it has even destroyed the existing computing environment.
To tackle and keep your environment free from vulnerability, it is very important to have a strong Cyber Security Governance in place. Ensuring cyber security requires coordinated efforts throughout an information system which needs to be backed up by and adequate Cyber Insurance Policy.
Cyber Insurance come into play when after taking all the security measures still your organization is attacked or hacked then the insurance policy in general covers your expense against any litigation or damages claimed by 3rd party.
In this article I have discussed different element of Cyber Security, how you find out vulnerabilities against your network or web security, what kind of measures you take and the Cyber Insurance checklist for your organization.
Elements of Cyber Security
Application Security – Application is the use of software, hardware and procedural methods to protect application from the external threats and vulnerabilities. This becomes an issue and an integral part during the development phase as application are most accessible over network. Security measures built in minimizes access, steal, modify and delete sensitive data.
Information Security – Information Security (IS) is a set of strategies for managing process, tools and policies to prevent threats. It is a set of business process that protects information assets regardless how the information is formatted or in transit. IS programs are build with an objective to maintain confidentiality, integrity and availability of business data. It is basically authorizing the view and handle of confidential data and resources.
Network Security – This is to ensure that there is no leakag e in the data flow or easy entry point for external force to get into your computing environment. This is the fundamental of all security as Network often use by the hackers to get into any system. Cyber Insurance policy might not protect your damage in case the network security was vulnerable.
Operational Security – Operational Security is an analytic process that classifies various assets and it protection from threats. IT operation are sometime gets effected by unexpected audit regulation, OS describes strategies to prevent potential adversaries from discovering critical operations related data. This security consists of five critical steps :
- Indentify Critical Information – The first step to determine critical & harmful data for the organization.
- Determination of Threats – Next is to determine all the possible threats to the organization. This could be internal as well as external. The objective is to ensure a full proof blue print of all possible threats.
- Analyze vulnerabilities – This is the stage to map all the resources to possible threats and identify the areas which has potential lapses and be the reason for vulnerability.
- Assess risks – This is the step which determines risks which are beyond control or unexpected. Mostly this deals with physical loss of any kind if there is so.
- Apply countermeasures – The final step is to lay down and implement a plan to mitigate all the above for a full proof security.
All the above is very important for Cyber Insurance claim. If proper IT security measures are not in place then claiming against your Cyber Insurance policy might not cover your claim situations.
Measures for IT Security
To deal with all the above there are various steps and methodology available. The most cost effective vulnerability tests recommend to every organization irrespective of its business nature are :
- Through Scanning - This includes a through scanning of your network devices, firewall, individual work stations and all possible ips. All the entry points using high quality software.
- System Security Planning - Once the risk areas are identified a detail cost effective and easy adoptable recommendation is recommended. This recommendation are related to implement various system and devices in place for prevention.
- Physical Security Planning – This is a plan where we create provision for physical losses. It ensures that even after the physical lose, the rebuild can be done and cost can be derived through the insurance coverage.
Cyber Insurance Cover Checklist
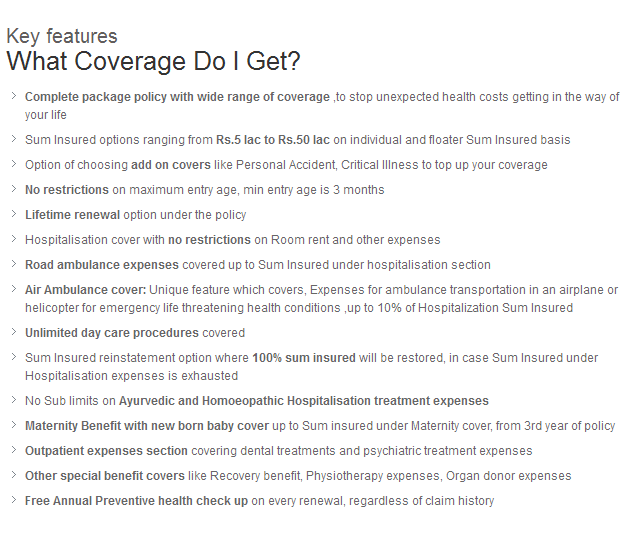
Before getting a cyber insurance policy we need to ensure that it covers the main concerns and protects and business loss in case any cyber attack takes place. A cyber insurance policy should cover first-party and third-party liability coverage to an organization when cyber-risk materializes and or cyber security controls at organization fails.
The coverages established by the cyber insurance shall cover property, theft and liability as represented in below section:
Property and Theft:
1) Destruction of software applications, data, systems and network
2) Unrecoverable loss of information of organization’s stored data
3) Recovery from malware or other malicious codes
4) Business interruption due to cyber-incident (Loss of net profit as a result of a material interruption to the insured’s network)
5) Denial of Service
6) Information Theft – Loss of control of customer’s data/record
7) Breach of intellectual property
8) Cyber Extortion and Cyber espionage
9) Losses due to cyber-terrorist acts
10) Harm to electronic media or data contents
11) Terrorism/War exclusion with carve back for Cyber terrorism
Liability:
12) Network Security
13) Private confidentiality breach/Data Liability
- Loss of personal information
- Loss of corporate information
- outsourcing
14) Reputational damage
- Repair of the organization’s & individual’s reputation
- Notification and Monitoring
15) Business continuity/supply chain disruptions
16) Crisis management and response to data theft (includes costs of administrative expenses i.e. forensic investigations, penalties, regulatory and governmental fines)
17) Cost of repairing, replacing and updating computer system
Limit of Liability:
This is the most important part of the your policy. You should get the maximum possible cover. You can’t claim more than your policy cover.
If you need any further information or looking to get a one to one consultation then feel free to contact us at info@gibl.in or call us at 033-6564-1850.